Stumbled across a quirky situation the other day, while using a script in Strange Brigade. The below is my script:
Code: Select all
[ENABLE]
aobscanmodule( GetBaseStuff, StrangeBrigade_DX12.exe, F64439??010F85????????803D????????000F85????????4885FF0F84????????486348??0F2F7C39 )
registersymbol( GetBaseStuff )
label( GetBaseStuff_o )
registersymbol( GetBaseStuff_o )
alloc( Hook, 0x1000, StrangeBrigade_DX12.exe )
label( pEntity )
registersymbol( pEntity )
label( dwEntityId )
registersymbol( dwEntityId )
label( pActor )
registersymbol( pActor )
Hook:
push rax
mov [pEntity],rdi
mov [dwEntityId],edx
mov rax,[rdi+8B0]
mov [pActor],rax
pop rax
GetBaseStuff_o:
readmem( GetBaseStuff, 5 )
jmp GetBaseStuff+5
pEntity:
dq 0
dwEntityId:
dd 0
pActor:
dq 0
GetBaseStuff:
jmp Hook
[DISABLE]
GetBaseStuff:
readmem( GetBaseStuff_o, 5 )
unregistersymbol( pActor )
unregistersymbol( dwEntityId )
unregistersymbol( pEntity )
dealloc( Hook )
unregistersymbol( GetBaseStuff_o )
unregistersymbol( GetBaseStuff )
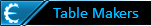
- before the script is enabled, the memory at the hook location looks like this:

- notice the address at which the array starts -> 14B2CBFF3; notice the protection -> Protect:Execute/Write Copy
- once you enable the script this happens:

- notice how protection changes to -> Protect:Execute/Read/Write
- if you now click on the C2 byte and scroll the window, you'll find that past our write, the rest remains to Protect:Execute/Write Copy
- also notice how the C2 byte is now part of a 00-aligned address, starting a new memory block -> 14B2CC000

- if you now disable the script, which restores the 5 hooked bytes back, this happens:
- CE restores the bytes, but it doesn't restore the protection; considering the array of bytes we search for spans across the end of a memory block and start of another memory block, any type of scan will now fail

The solution is to force CE to copy more bytes via readmem to include at least 1 byte from the next block of memory (that C2 +1). So I chose this:

And now the script looks like this:
Code: Select all
[ENABLE]
aobscanmodule( GetBaseStuff, StrangeBrigade_DX12.exe, F64439??010F85????????803D????????000F85????????4885FF0F84????????486348??0F2F7C39 )
registersymbol( GetBaseStuff )
label( GetBaseStuff_o )
registersymbol( GetBaseStuff_o )
alloc( Hook, 0x1000, StrangeBrigade_DX12.exe )
label( pEntity )
registersymbol( pEntity )
label( dwEntityId )
registersymbol( dwEntityId )
label( pActor )
registersymbol( pActor )
label( GetBaseStuff_ext )
registersymbol( GetBaseStuff_ext )
Hook:
push rax
mov [pEntity],rdi
mov [dwEntityId],edx
mov rax,[rdi+8B0]
mov [pActor],rax
pop rax
GetBaseStuff_o:
readmem( GetBaseStuff, 5 )
jmp GetBaseStuff+5
GetBaseStuff_ext:
readmem( GetBaseStuff, 15 )
pEntity:
dq 0
dwEntityId:
dd 0
pActor:
dq 0
GetBaseStuff:
jmp Hook
[DISABLE]
GetBaseStuff:
//readmem( GetBaseStuff_o, 5 )
readmem( GetBaseStuff_ext, 15 )
unregistersymbol( GetBaseStuff_ext )
unregistersymbol( pActor )
unregistersymbol( dwEntityId )
unregistersymbol( pEntity )
dealloc( Hook )
unregistersymbol( GetBaseStuff_o )
unregistersymbol( GetBaseStuff )
Hope this helps those lucky enough to trip over this
Best regards,
Sun